I can only post 2 links. I modified my external links and posted the raw captures and the PCB picture in comments.
Frequency: 315MHz, 390MHz
Modulation: Amplitude Modulation (AM)
FCC ID: HBW7964 (link 1)
IC: 2666A-7964 (link 2)
Device Model: 953EV/EVC
Manufacture Date: 02/15
Other Information:
- 3 buttons
- Link below contains information for decoding Sec+ 1.0 and 2.0. (link 3)
- Only capturing for 315MHz because 390MHz seems to only be for legacy devices (link 4)
Auto Hopping Read
Button 1 - Tied to Chamberlain garage door motor
Security+ 1.0 42b 315AM
key: 0x917E94EF0000A578 ## This changes at different points in time
id1:1 id0:1 Btn:left
Sn:0x056380C6
Cnt:0xA578 ## This changes at different points in time
Sw_id:0x1
Button 2 - Not tied to anything
Security+ 2.0 62b 315.00 AM ## This seems to do both 315MHz AM and 390MHz AM
Pk1:0x3C045F2FB714 ## This changes at different points in time
PK2:0x3D105753A3D0 ## This changes at different points in time
Sn:0x7F84B164 Btn:0x21
Cnt:0xE500055 ## This changes at different points in time
Button 3 - Not tied to anything
Security+ 2.0 62b 315.00 AM ## This seems to do both 315MHz AM and 390MHz AM
Pk1:0x3C282C125BB2 ## This changes at different points in time
PK2:0x3D06AE335EAD ## This changes at different points in time
Sn:0x7F84B164 Btn:0x20
Cnt:0xE500050 ## This changes at different points in time
Links:
Link 1 - FCC ID Info:
Link 2 - Industry Canada Info:
[https://]industrycanada[.co]/2666A-7964
Link 3 - Chamberlain Sec 1.0 and 2.0 Reverse Engineered:
Link 4 - Chamberlain Frequencies:
[https://]support.chamberlaingroup[.com]/s/article/How-to-get-my-old-garage-door-opener-on-the-same-frequency-as-my-new-opener-1484145611617
Attachments:
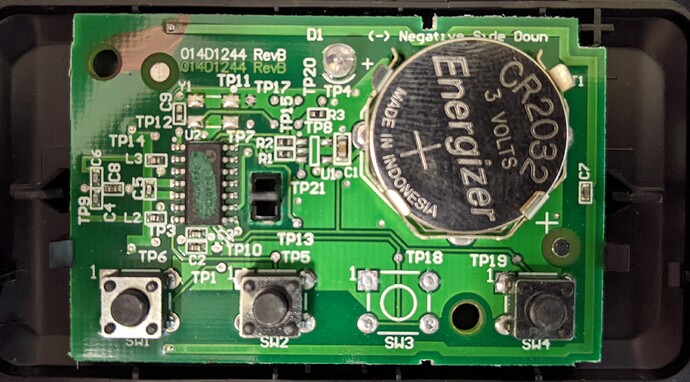
Garage Remote Board.jpg - This is a picture of the garage remote PCB
Button1.sub - Raw capture of button associated with my garage door. Physically labeled with a 1 on the button.
Button2.sub - Raw capture of button 2. Not associated with anything. Physically labeled with a 2 on the button.
Button3.sub - Raw capture of button 3. Not associated with anything. Physically labeled with a 3 on the button.