The flipper is able to scan things like credit cards, but is unable to emulate the UID as of right now. Will there be support added for emulating NFC cards in the near future?
Yes, probably in the coming few weeks
I see the emulation is now being added in the dev channel.
I’ll be testing this in the next couple days. I’d did notice that when I launch the emulator from the Favorites link it says “Emulating MF Classic”, where as the the 125 khz RFID emulator says " Emulating filename "
As I know this is just under development, is the final version planned to display the file name like the other emulator so we can readily identify the tag being emulated?
Just wanted to ask in the event there is a different developer working on this module. I believe having the file name displayed is an asset and would provide a consistent feel between the different emulators.
Cheers
The mifare classic emulation is kinda working, but we’ve faced some really tough problems with the timings due to the fact that our NFC chip doesn’t natively support Mf classic emulation, and our CPU clock can’t be divided evenly into 13.56mhz chunks. This means that the emulation will only work with some readers, but most if them will not accept it due to the answer coming too late. We’ll be researching how this can be mitigated, but there’s a real chance that the emulation state will remain like that.
Thanks for the update! Unfortionate discovery that I am hopeful there will be a solution to given the prevalence of mifare technology.
Btw. The community appreciates everything the team is doing. I’ve seen great progress in this project and your team’s communication here on the forums has been exceptional!
Best to everyone.
I gave this a try tonight and had no luck. Current release firmware (0.59.1)
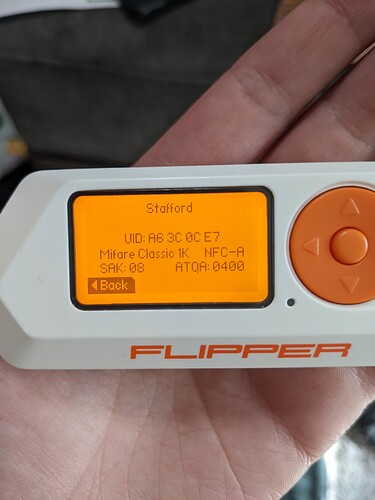
I have an NFC lock that uses a Mifare Classic 1K, all default keys, just UID authentication. Using my Proxmark, I am able to clone that card and emulate it.
The Flipper reads the card and correctly identifies it, but the emulation fails. The lock doesn’t even recognize it as a Mifare Classic; it will buzz when an invalid card is presented, but it doesn’t even do that. It acts like there is no card there.
While the Flipper is emulating, the Proxmark reads the UID, ATQA, and SAK properly, but cannot actually read all of the sectors, and thus I cannot even get a dump to save and compare to the card dump.
As I said above, this is a known issue and we can’t do anything about it at the moment. You can patch your proxmark3 to ignore read timings and it’ll work, but if your reader has a correctly implemented mifare classic protocol and respects proper timeouts - our emulation will not work.
I was able to scan and run the app to look for keys on my Mifare Classic 1k card.
When emulating the reader does not beep or turn green.
The LED on my flipper stops blinking when I put it up to the reader.
Is this still due to the WIP?
You are emulating the UID only, not the whole card. It means that the dump might be incomplete or you’re using the wrong file (output of the initial read instead of the long one)
I actually have both keycards stored. I just realized you are correct and I only emulated the UID, however the 2nd where I had it find the keys; it only found 1 key in sector A. And has same behavior
This means that this card’s keys are not in the dictionary we use. You’ll need something like a proxmark3 to perform a more computationally-intensive attack like nested/hardnested to recover other keys, and then you can dump the card and convert it to FFF (Flipper File Format) using this script
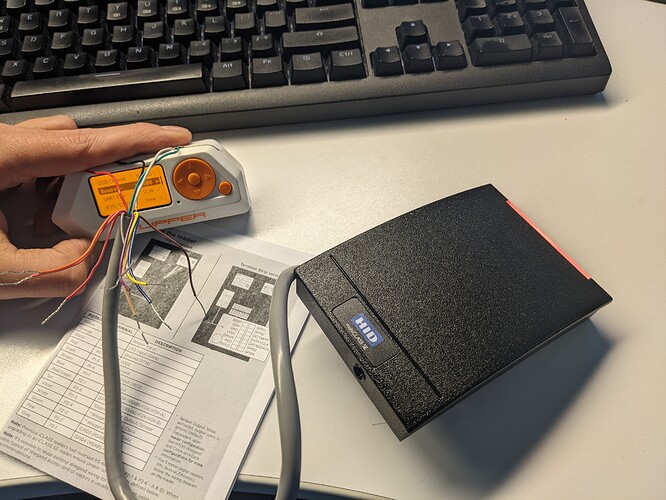
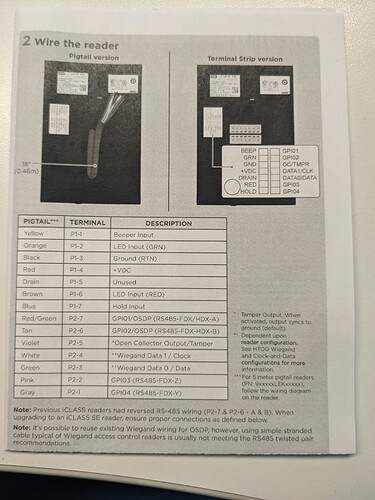
I have an abundance of HID RP40 readers and arduinos. Can I make my own proxmark with this HID reader and an arduino mega or uno? Can i use the gpio on the flipper? i only need 4 wires for these readers to interface serial.
No, a proxmark uses an FPGA and not a microcontroller. DIY-ing it is basically not an option, sadly.
@Astra : Nice, i wrote something simular for converting Proxmark json to flipper
see prox2flip.py in https://github.com/evilpete/flipper_toolbox
@Astra does the new mifare classic emulation emulate the contents of the card or just the UID at the moment?
The whole content of the tag.
Sorry, but I have to ask:
Mifare tags are supposed to encrypt their data sectors, right? From what I see, the keys stored on the tag are not readable. So unless the tag uses a simple default key, how are you going to emulate the whole content of the tag?
Dictionary brute-force attack on keys. On the future we’ll add nested and herdnestwd attacks to recover all keys on any card where at least one key is known (it’s based on the mathematic vulnerability of the protocol)
Hi, I just ordered my Flipper (second production batch expected to be shipped from August 2022 onwards).
When I read that you’re not sure that the Flipper might ever be able to emulate Mifare Classic Cards because of CPU constraints, that scares me because it is, for me, the most useful feature.
Is there a plan to correct that for the next Production batch to make sure it will be able to emulate such cards ? (if it ends up not being able to do it with software updates?).
Thanks,
I think the flipper team has already done a phenomenal job in figuring out a workaround for that issues. The current state of the mifare 1k full dump emulation has worked for multiple lock systems that I have tested on so far.